The fediverse, also known as the open social web that includes Mastodon, Meta’s Threads, Pixelfed, and other apps (…)
Mention Lemmy for once 😠
Meta’s Threads
LOL
We are tiny in comparison to the rest of the fediverse.
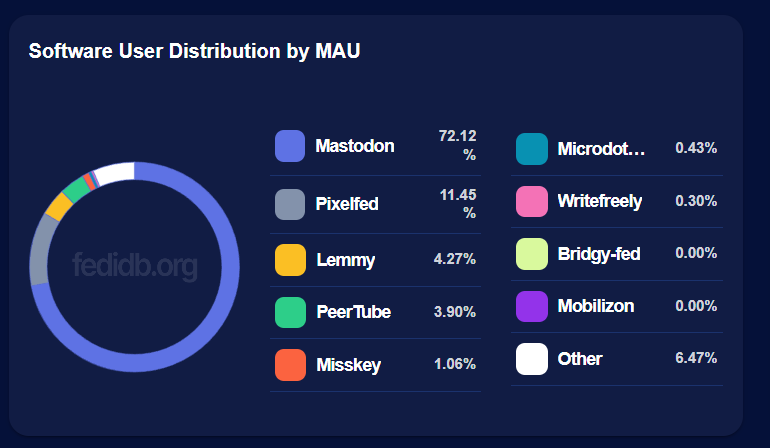
But its actually usable, pixelfed sucks, prob way more actual engagement and conversation here, pixelfed is hella ppl posting with no likes or views
I mean, discoverability is hard, sure, but add a few hashtags and you can get a lot of people to see your posts. also, mentioning a lemmy group as a user posts your post to the community.
deleted by creator
Yeah!
I asked here about that and was told there’s not enough of us here. Meh.
Funny how that works. Wonder if not mentioning it will help remedy that?
Also Lemmy: Here’s a bunch of death threats and pictures of a pig taking a shit because you said democracy was a good idea
Was the first paragraph written by the Meta marketing department?
Yeah, there’s also this:
A more recent issue came about when Pixelfed’s creator, Daniel Supernault made the details of a vulnerability public before server operators had a chance to update, which would have left the fediverse vulnerable to bad actors, she says. (Supernault has already apologized publicly for his handling of the issue that had affected private accounts.)
In the case of the Pixelfed issue, for instance, the Hachyderm Mastodon server, which has over 9,500 members, decided it needed to defederate (or disconnect from) other Pixelfed servers that hadn’t been updated in order to protect their users.
It is weird to spend almost half the words in this, pretending that something in Pixelfed that wasn’t a problem on Pixelfed’s side was. This is the weirdest “vulnerability” in the world to pick if you want to pick one to hold up extensively as an example.
Regardless whether you want to pretend that not caring about Mastodon is a valid defense when implementing software using the ActivityPub protocol, that still doesn’t change anything regarding how Dansup handled the disclosure of the effects it had.
- This is nothing to do with ActivityPub. It’s to do with Mastodon’s custom implementation of “private” posts.
- Making it extremely clear to everyone that random server software can expose Mastodon’s “private” posts is absolutely the right way to handle disclosure here. Dan didn’t even try to do that, he just fixed the bug, but if he had made a big post saying “hey this is not my fault Mastodon private posts are not private, here’s full explanation about what’s going on” I think that would have been completely fine. This is not a “vulnerability” in the traditional sense like a buffer overflow, it’s just a design flaw in Mastodon which other softwares are by convention agreeing to cater to. I think the culture of security (and the level of clue in general) in the Fediverse has wandered into territory where “let’s all pretend that these posts are secure and get mad at anyone who reveals that they are not” is widely accepted now, but that doesn’t make it right.
It has everything to do with ActivityPub since if you follow that protocol strictly you will cause this behavior. It still doesn’t change that Dansup was told that this caused Bad Things™ and yet he didn’t follow normal procedure in how you handle it.
Vulnerabilities don’t need to be buffer overflows.
/cybersec researcher
It has everything to do with ActivityPub since if you follow that protocol strictly you will cause this behavior.
Absolutely not. Which part of the spec? I linked up there to quite a thorough explanation of what the spec does and doesn’t dictate in this area, and how Mastodon chooses to behave in its implementation. What part of my explanation did I get wrong? Are they violating 5.1, 5.2, 7.1, some other part? How?
/cybersec researcher
I do not believe you. “I’m sending things out which need to be handled carefully in a protocol-nonstandard way by the recipient server software (which could be literally anything), or else my user’s private posts will be exposed. If someone talks about that situation and lets people know what’s going on, that’s irresponsible disclosure.”
If you actually are a cybersec researcher, you are bad at your job.
hahahahaha
Watch and try again ;) I post under my real name.
https://www.cve.org/CVERecord?id=CVE-2024-44754
https://www.youtube.com/watch?v=ZbKLAjPYOEg
Feel free to post less and read more.
Okay. What part of the spec did Pixelfed violate? Where in the spec is Mastodon’s implementation of private posts justified?
I usually agree with you, but here @[email protected] is right.
Full disclosure
With the full disclosure approach, the full details of the vulnerability are made public as soon as they are identified. This means that the full details (sometimes including exploit code) are available to attackers, often before a patch is available. The full disclosure approach is primarily used in response or organizations ignoring reported vulnerabilities, in order to put pressure on them to develop and publish a fix.
This makes the full disclosure approach very controversial, and it is seen as irresponsible by many people. Generally it should only be considered as a last resort, when all other methods have failed, or when exploit code is already publicly available.
Responsible or Coordinated Disclosure
Responsible disclosure attempts to find a reasonable middle ground between these two approaches. With responsible disclosure, the initial report is made privately, but with the full details being published once a patch has been made available (sometimes with a delay to allow more time for the patches to be installed).
Hm… maybe. The exact nature of the problem in Pixelfed means that anyone with a Pixelfed account on a server which is getting private statuses can choose to follow someone who’s set to “approve followers” and then read all the private statuses. I do see how that’s significantly worse than just the normal lay-of-the-land of the problem, which is a little more random, and laying that out as a little roadmap to read someone else’s private statuses before there’s been a nice responsible length of time for things to get fixed could be seen as worsening the problem.
The point that I’m making is that anyone who’s posting private statuses to Mastodon and expecting them to stay private is making a bad mistake already. The structure of the protocol is such that they can’t be assured of staying private regardless of what Pixelfed did or even if Pixelfed didn’t exist. They’re getting federated to servers whose behavior is not assured, in a way where a conformant ActivityPub implementation can expose them. People who are posting private statuses need to understand that.
That whole blog post where the person is talking about her partner writing private statuses, and then the gut-wrenching realization that they were being exposed on Pixelfed… but then the resolution being “Pixelfed fucked up I hate Dansup now” and then continuing to post the private statuses, is wrong. That person’s partner needs to stop treating their private posts on Mastodon that way. The timer for responsible disclosure started circa 2017 or whenever Mastodon decided on how to implement their private statuses. It’s been and gone.
Like I say, I get the harm-reduction aspect of saying it would have been better if Dansup was a little more discreet about this particularly bad attack vector until a few more days went by for everyone to upgrade. But it hardly matters. There are still server softwares our there that are going to be exposing people’s private Mastodon posts. It’s just how federation between untrusted servers works. Giving people the illusion that if Dan had just been more discreet then this harm would have been reduced is lulling them into a false sense of security, in my view.
If you know of other ActivityPub servers that expose private posts the same way I suggest you make a responsible disclosure to the developers.
I don’t know of any, but you claim they exist so …
Are you hoping to restart our disagreement through sheer passive-aggressiveness? Okay, sure.
In my view, this is a Mastodon design flaw (or a user-expectation issue or whatever you want to call it.) I already said that, and you’re involved in the unproductive-arguer’s pastime of pretending not to understand that that’s my position, and just aggressively repeatedly reframing things according to your position and hoping I’ll knuckle under to it through sheer force of repetition.
I’m not super invested in trying to track down each and every software that might manage to expose the “private” statuses in this way. I just know that as things come and go there are guaranteed to be some. If you have an mbin account and Mastodon account, though, we can try a little experiment. I don’t know the outcome, I’m just curious after taking a quick look down the FediDB list and a quick grep through mbin’s source code. You can be the one to responsibly disclose to mbin how their ActivityPub-conforming behavior is a problem, if indeed it turns out that it is, since you seem to be extremely committed to the idea that the model of “vulnerability” needs to be applied to this particular ActivityPub-conforming behavior. Since you’re a security researcher, having that as a CVE you discovered can be an achievement for you. It’s all yours, you can have it.
Maybe I’m wrong, but shouldn’t posts only be insecure if they’re propagated to the insecure instance? Is any private post visible to people on servers that the poster doesn’t have followers on?
Could Icurlthe uri of a post thats “private” and get the post’s content?Maybe I’m wrong, but shouldn’t posts only be insecure if they’re propagated to the insecure instance?
“Insecure” in this case simply means any server that doesn’t implement Mastodon’s custom handling for “private” posts. With that definition, the answer to your question is yes. It has been mentioned by Mastodon people that this is a significant problem for the ability to actually keep these private posts private in the real world. The chance of it going wrong is small (depending on your follower count) but the potential for harm is very large. I would therefore go further, and say that it’s a very bad thing that Mastodon is telling people that these posts are “private” when the mechanism which is supposed to keep them private is so unreliable.
https://github.com/mastodon/mastodon/issues/712
Is any private post visible to people on servers that the poster doesn’t have followers on?
It is not. If you’re sufficiently careful with approving your followers, making sure that each of them is on an instance that’s going to handle private posts the way you expect, then you’re probably fine.
Could I curl the uri of a post thats “private” and get the post’s content?
If it’s been federated to an insecure server then yes. If not then I think no.
Mastodon really is the internet explorer of the fediverse.
In any case, I don’t think its that bad. I would compare it to an email provider accidentially leaking messages. Still bad, but its not a reason to abandon email as a means of communication.
We should encrypt posts, like diaspora does. Like how we should pgp encrypt emails, but no one will.also, I just checked myself, a random “private” post I made isn’t accessible over AP if I curl it unauthenticated. Running
curl.exe https://calckey.world/notes/a63slz8j6l -H "Accept: application/activity+json"returns nothing, but replacing the uri with a public post does show it.
An insecure server’s copy of the post isn’t accessible over AP, only the original post’s link should return anything.
I still feel that interoperability between mastadon and Lemmy is kind of messed up. How to browse a Lemmy community through mastodon application?
You cannot use a mastodon app as a lemmy client, but you can view lemmy communities by opening them as if they are profiles. For example, open @[email protected] and it will show up as a user, but it will be the communitiy’s posts.
You can mention it in a post to forward the post to the community as well.
It’s terrible
I can’t wait to find out which project has the most security holes 🔥
Any guesses?
The ones with the most amount of code lines and dependencies probably. More code = more problems.
IMO poor security is more about a lack of eyes on the code. Projects that have a single developer and a lower user-base will be pretty easy money.
…that will pay those who responsibly disclose security vulnerabilities that affect fediverse apps and services.
If it is straight to the project, then I’m all for it. Otherwise, it seems sus.
It is to the person who discovers the vulnerability. That’s fairly normal… how would giving it to someone else motivate the result they’re trying to get?