AMD-SB-7005 “Return Address Security Bulletin” outlines this new speculative side channel attack affecting recent EPYC and Ryzen processors.
AMD has received an external report titled ‘INCEPTION’, describing a new speculative side channel attack. AMD believes ‘Inception’ is only potentially exploitable locally, such as via downloaded malware, and recommends customers employ security best practices, including running up-to-date software and malware detection tools. AMD is not aware of any exploit of ‘Inception’ outside the research environment, at this time.

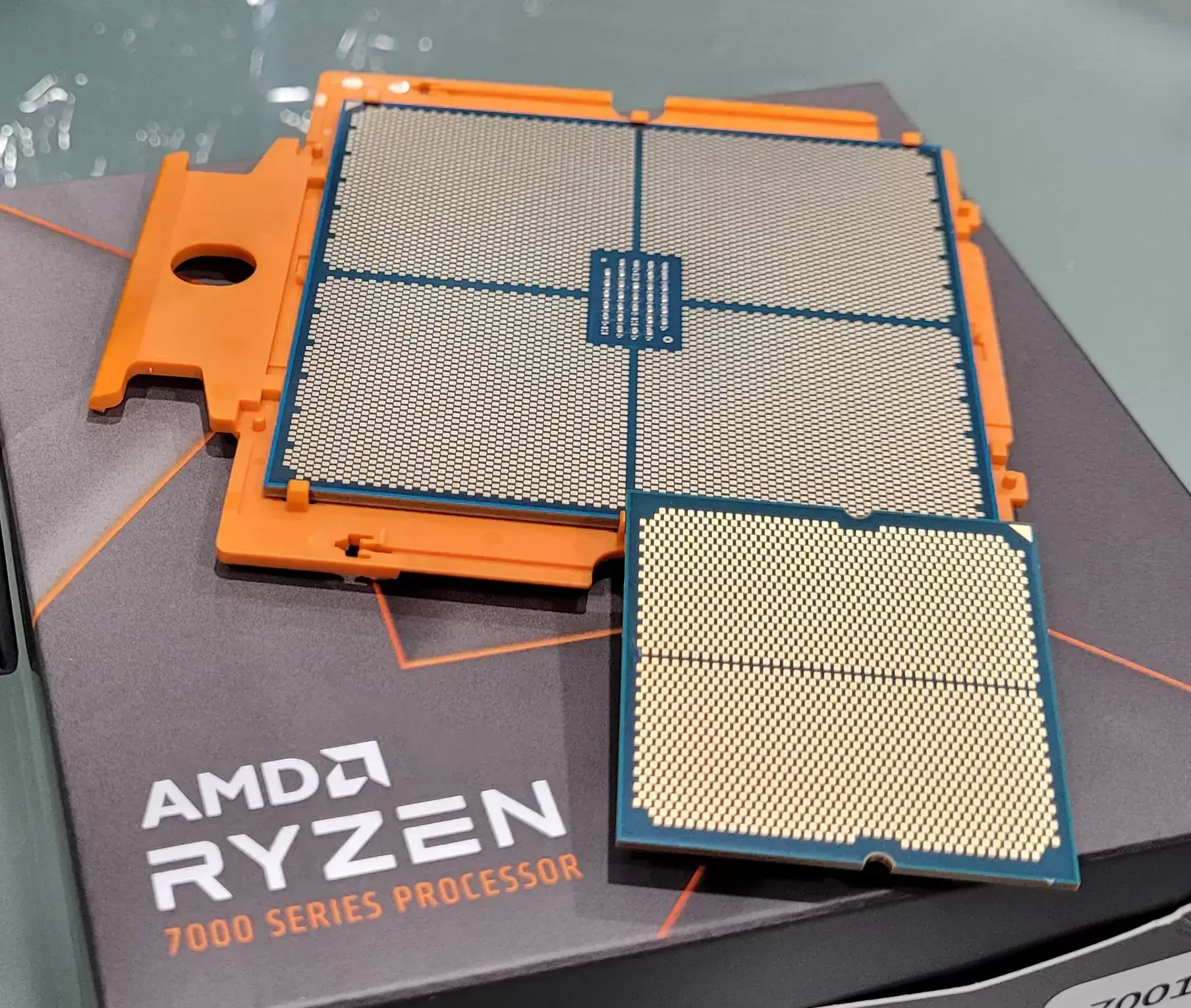
How is getting more performance out of a CPU greedy? Is making a better product that people want greedy? Stagnation is lazy, and making CPUs faster is better for the consumer. So is AMD putting pressure on Intel by releasing faster and faster CPUs. This is a large part of why we have such powerful computers now that shape our modern world.
What “hack” are you talking about that they implemented in Zen 3? Speculative Execution has been around for years, and speculative execution vulnerabilities have been happening ever since. Thankfully, the fix is available and not incredibly difficult to implement, which seems to be the case for most of these bugs. Why should we sacrifice speed for the potential that maybe we implement a bug that can be fixed with a BIOS upgrade?
Getting more performance is not greedy. What is greedy is adding hacks for performance for $$$'s which is greedy considering the security nightmares that come with it. Also, how the hell are you supposed to update your BIOS if it’s not supported by
fwupdand you can’t use Windows?Also, what Zen 3 added was not flushing what Zen 2 flushed.